...
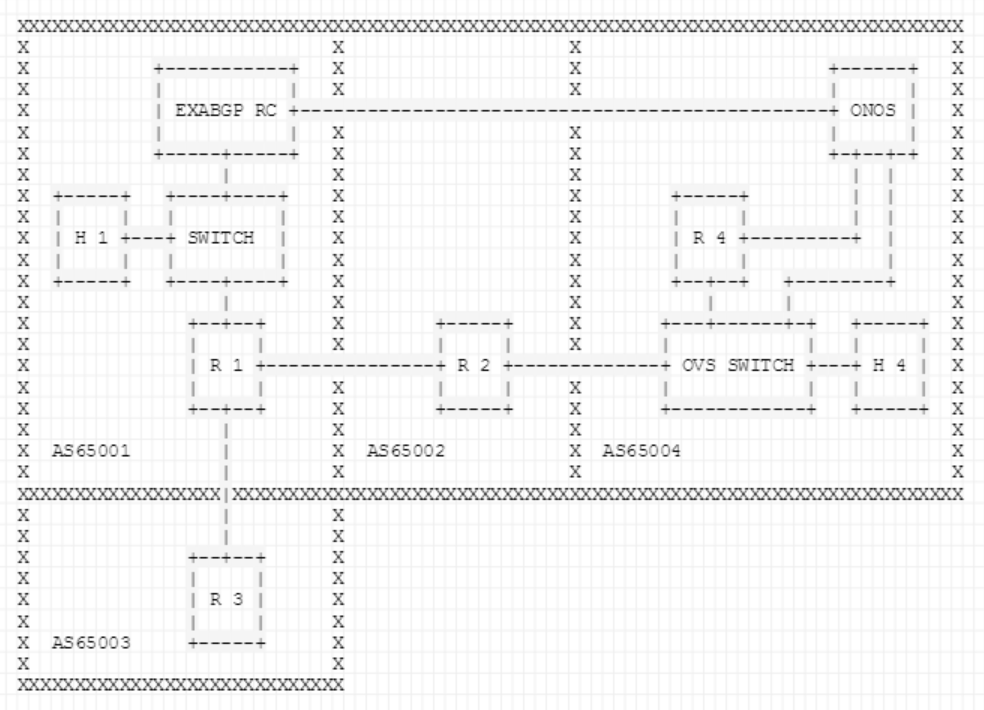
Figures 2 and 3 show the topology that is setup via the topo.py file inside the tutorial folder (TODO: set exact location). The BGP speakers are Quagga routers and the route collector is an ExaBGP router running a custom script to replicate the behavior of a RIPE route collector.
...
...
...
Fig. 3: The full emulated demo topology.
AS65001
Intermediate AS that consists of a BGP speaker (R1), a L2 switch, a host (H1) and an ExaBGP Route Collector (RC).R1: Announces 10.0.0.0/8 and is a neighbor of AS65003 and AS65002. Also, it has the exaBGP RC as an iBGP neighbor and propagates BGP update messages to it.
ExaBGP RC: RC connected to R1 but also to the ONOS controller on the protected AS (in real world this connection is done through the underlying network; the only limitation is that the IP endpoint of ONOS should have a non-hijacked IP address so that the monitor can reach ONOS during the hijack).
H1 / 10.0.0.100: Host which is going to be communicating with the host inside the protected AS. It is used to provide us a visualization of the data-plane behavior when the BGP hijack occurs.
...