...
| Code Block | ||||
|---|---|---|---|---|
| ||||
$ cd onos/tools/tutorials/artemis $ sudo ./topo.py |
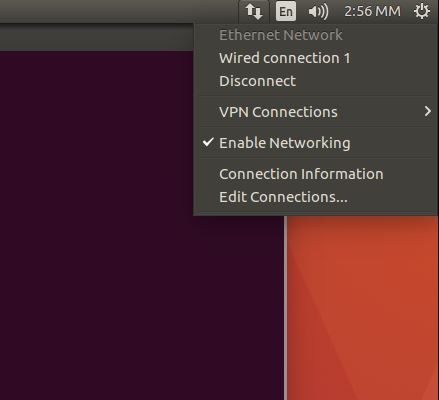
Note: If you are using a GUI version of Ubuntu, you should uncheck "Enable Networking" in the relevant menu, as shown in Figure 3, in order to avoid interfaces swapping IP addresses!
Fig. 3: Uncheck "Enable Networking".
While having the two terminals open(ONOS instance and mininet), open a new terminal and load the network configuration with onos-netcfg. From this terminal, login to the ONOS CLI:
...
| Code Block | ||||
|---|---|---|---|---|
| ||||
mininet> xterm R3 (opens a new windowterminal on R3 node) R3>mininet> telnetpingall localhost bgpd(to make the hosts visible) mininet> h1 ping h4 (to see the data plane interactions) |
2. On the new terminal of R3, announce 2. Announce the prefix:
| Code Block | ||||
|---|---|---|---|---|
| ||||
R3> telnet localhost bgpd
Password: sdnip (this is the password)
bgp> en (enable)
bgp# conf t (configure terminal)
bgp(config)# router bgp 65003
bgp(config-router)# network 40.0.0.0/8 |
Now the hijacker (AS65003) will attract all the traffic away from AS65001 (destined to 40.0.0.0/8); at the same time, the ExaBGP speaker will send the BGP update of the hijack (among other updates seen by AS65004) to the ONOS instance (running ARTEMIS) and the hijack will be detected. Checking the logs, you will see that the attack is actually detected and the deaggregation mechanism has successfully mitigated the attack (by announcing the more specific prefixes 40.0.0.0/9 and 40.128.0.0/9 from the BGP speaker of the protected AS). After BGP converges and the control and data planes are consistent, the traffic of AS65001, destined to 40.0.0.0/8, returns to the protected AS, as shown in Figure 5.
Demo video
Fig. 5: Successful mitigation of the BGP prefix hijacking attack, with a data loss of only 4 packets.
3. Also, by checking the current configuration of R4, following similar steps as for R3:
| Code Block | ||||
|---|---|---|---|---|
| ||||
mininet> xterm R4 (opens a new terminal on R4)
R4> telnet localhost bgpd
Password: sdnip (this is the password)
bgp> en (enable)
bgp# sh run (show running configuration) |
You observe that ARTEMIS has automatically configured R4 to announce the more specific prefixes 40.0.0.0/9 and 40.128.0.0/9, thus mitigating the attack, as shown in Figure 6:
Fig. 6: Current configuration of R4.
Demo video using GNS3 as emulation platform
Fig. 7: The fully emulated GNS3 Fig. 5: The fully emulated demo topology.
| Widget Connector | ||
|---|---|---|
|
...